If you are on Twitter you surely know that the topic that has been trending in the last weeks has been…well, Twitter. The twitterverse has been thrown into a healthy, comical, and not always accurate debate around freedom of speech, corporate responsibility and the implications of the $44 billion purchase by the world’s most loved/hated entrepreneur, Elon Musk.
We wanted to join in on the debate, specifically from the angle that we know best, identity! Last week we had the fortune to have our friend Scott McNealy join us to weigh in on this topic among many others. If you missed it, check it out here.
One of the biggest challenges that Mr.Musk will have to deal with as he takes on Twitter will be how to tackle the number of unauthenticated accounts, bots and bad actors on the platform. Twitter has some authentication (in particular verifying businesses, governments, and public figures) but it is abysmal at best. As Scott says in our discussion, “anonymity breeds irresponsibility but without it we don’t get the full truth”. Herein lies the catch. If you allow your mind to wander on the idea of what you might do without anyone knowing it is really you, well… you see where I am going (and you should watch the webinar to see where Scott goes!). It is this challenge that drives distrust in social media platforms, but the solution isn’t always easy to find.
One clear step forward would be to approach the topic of trust straight from the identity space. It seems relatively obvious as the identity world has been solving the issues of authentication for years, but the discourse of identity and accountability is much more of a blue ocean. And what better place to test its application than in the current public obsession of “free speech”? How do you bring the “digital you” to the discussion? How do you trust the other “digital yous” in the dialogue? Does this authentication drive accountability, influencing a more civil discourse?
The case for accountability is not only compelling from a social standpoint but also from a financial angle. It also seems to be clear as a next step for twitter and one that Scott says he mentioned to Elon already: providing authenticated spaces for groups of all types - vetted individuals that ensure a level of trust that can ultimately drive more productive dialogues. These authenticated spaces sitting alongside Twitter as it currently exists, seems like a natural move for Twitter to start becoming a more trusted platform for the online community.
And at the heart of it all lies the technology that many people take for granted - how to prove you are who you say you are and that you are allowed to do what you say you want to do - that’s Identity and Access Management. Beyond that - how do you, as a consumer, a member of twitter, a human-being - remain in control of the data you share? That’s also Identity and Access Management.
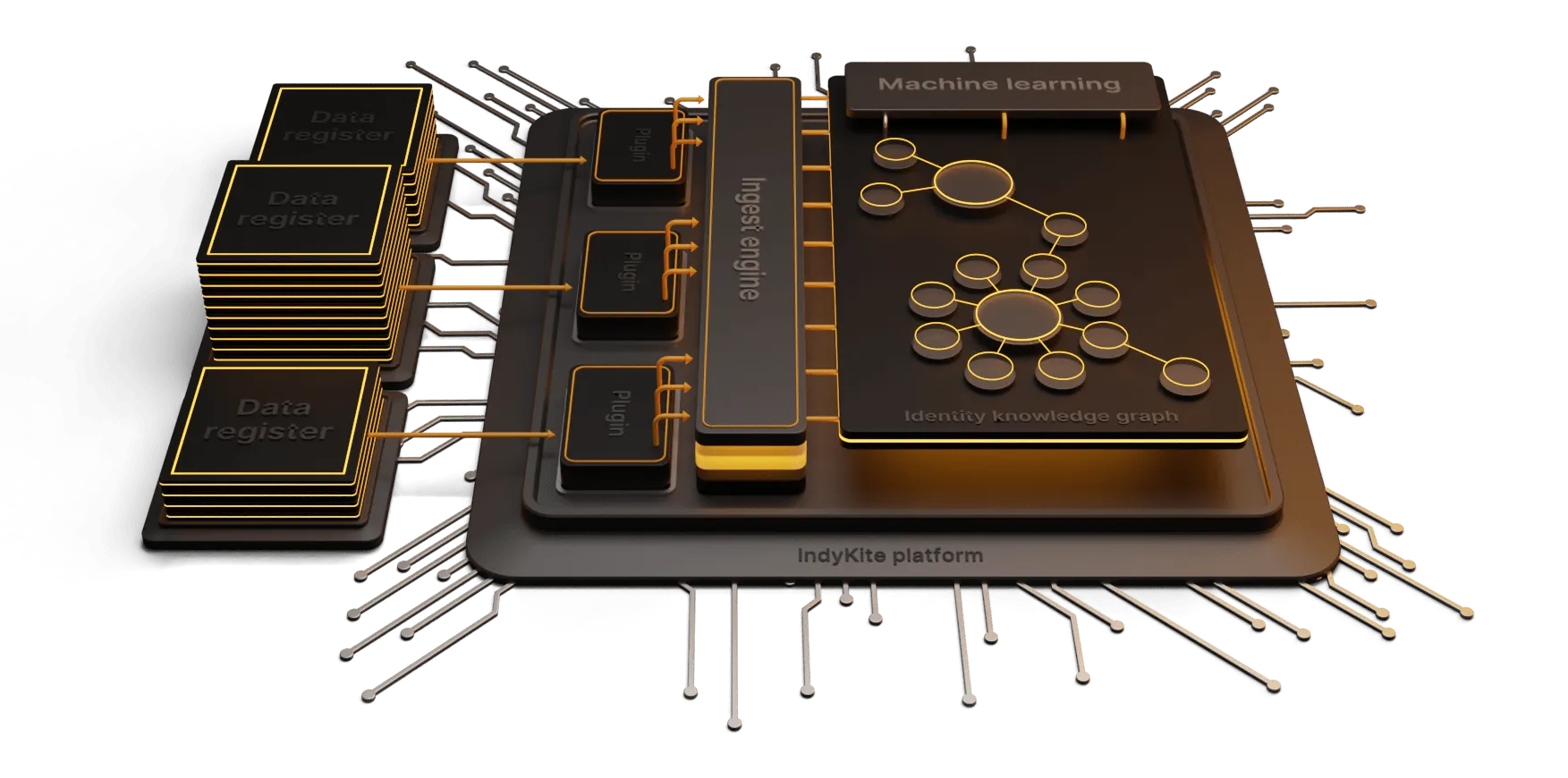
Sounds simple but it is actually quite complex! Come check out how the team at IndyKite is approaching these issues at our website.
And check out the full conversation with Scott here.