Graph has a unique ability to understand dynamic and complex relationships and manages data in a more natural, intuitive way, giving context to otherwise meaningless information. When applied to identity data, this can result in a number of ways that businesses can realize value, turning a former liability into a business asset.
How graph works with identity data
Businesses collect data about objects, things, and people. Most often, this information is stored in a traditional relational database or even a mainframe. In the graph, this information is called a node. Between each node is a link that represents the relationship between nodes, resulting in a new category of collected data - the data of relationships. Traditional databases can’t capture data about the relationship *between* things.
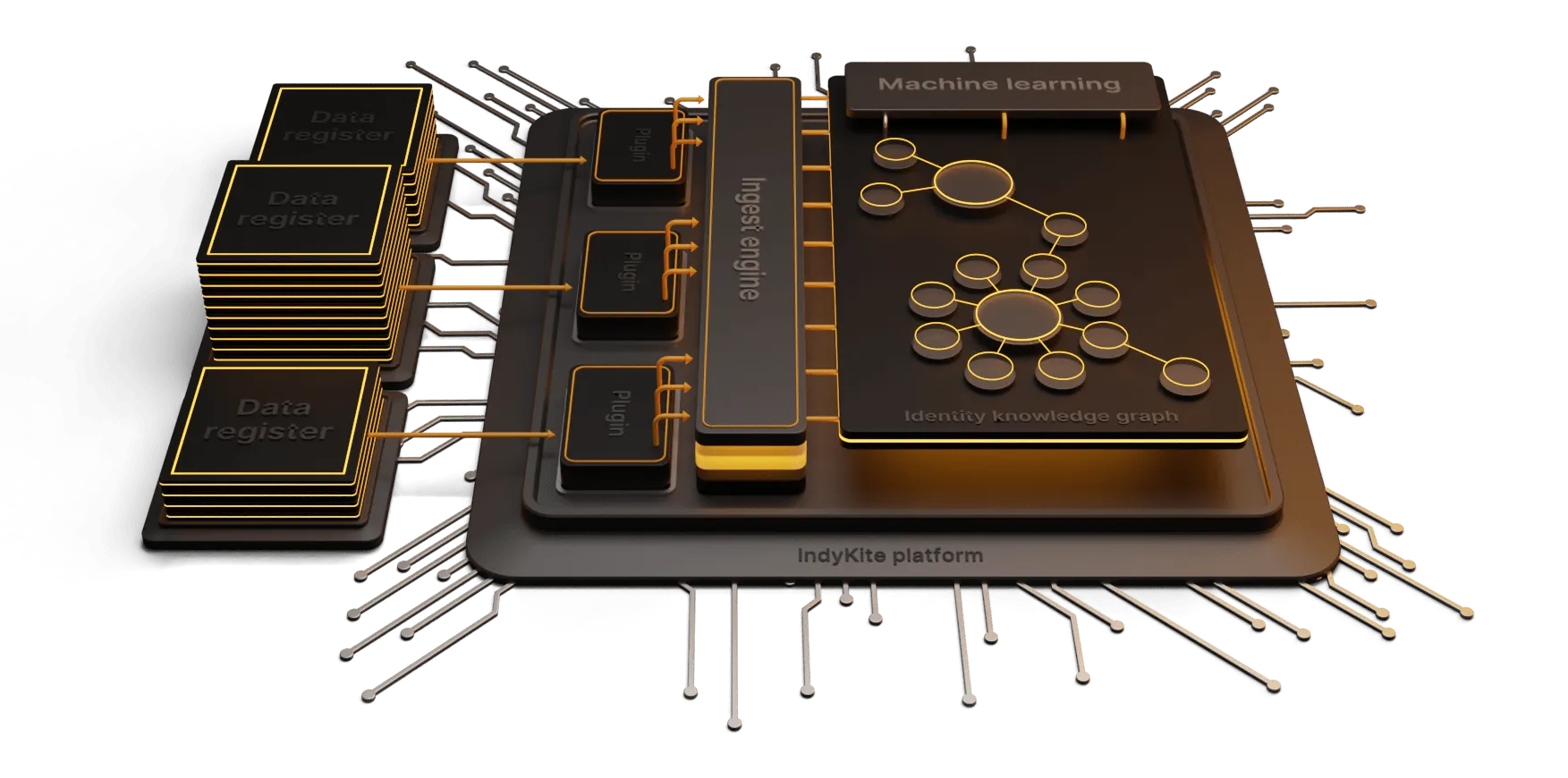
At IndyKite, we use graph technology to explore relationships between IoT and human identity in order to innovate identity and access management (IAM).
IAM solutions work by storing data on users, systems and the rules governing access to those systems. These rules determine who can access a system and what they are authorized to do.
By deploying a graph approach to IAM, the system can store complex, connected access control structures in a fully scalable way. Combining this flexible data model, with the capture of rich metadata for every element in a system, provides a whole new level of data management and the opportunity to apply machine learning to uncover rich data intelligence.
Creating value from identity data
Regulatory challenges, overly complex authorization policies and retrofitting legacy programs to meet new business needs are just some of the challenges modern businesses face with their IAM infrastructure.
A graph based approach can remove these obstacles, reduce risk for business through externalized authorization, while bringing context to the authorization data, driving better decisions and actions.
In addition, graph driven IAM systems are fully scalable (well into millions of elements), interoperable and lightweight.
This equates to faster systems, more efficient management, less friction for clients (shorter time to value) and the opportunity to create value from the data intelligence. This intelligence can drive more personalized services and offers, enhancing your client experience and growing your revenue.
We are firm believers in creating value from your identity and access system and seeing an immediate return on investment, rather than treating identity data as a business risk.
Want to learn more? Check out our webinar on Connected dots: Data graphs for digital identity.